Technology Stack
Mobile devices share some architectural similarities with their desktop counterparts, but there are significant distinctions between personal computers and these portable information systems. In addition to cellular functionality, including a number of radios, modern smartphones and tablets typically include a full suite of environmental sensors, cryptographic processors, and multiple wireless and wired communication methods. They also include a touch screen, audio interface, one or more high definition (HD) video cameras, and in odd edge cases unusual capabilities like video projectors.
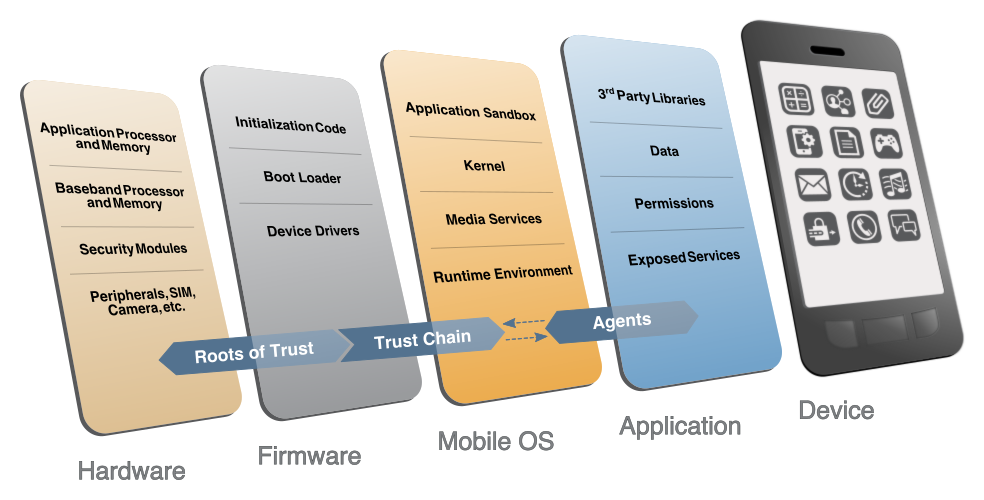
The figure below illustrates the mobile device technology stack, described in additional detail further below.
 Mobile Device Technology Stack
Mobile Device Technology Stack
For smart phones and tablets with cellular capabilities, a separation exists between the hardware and firmware used to access cellular networks and the hardware and firmware used to operate the general purpose mobile OS. The hardware and firmware used to access the cellular network, often referred to as the telephony subsystem, typically runs a real-time operating system (RTOS). This telephony subsystem is colloquially named the baseband processor, and may be implemented on a dedicated System on a Chip (SoC), or included as part of the SoC containing the application processor also running the general purpose mobile OS.
The firmware necessary to boot the mobile OS (i.e., bootloader) may verify additional device initialization code, device drivers used for peripherals, and portions of the mobile OS – all before a user can use the device. If the initialization code is modified or tampered with in some manner, the device may not properly function. Many modern mobile devices contain an isolated execution environment, which are used specifically for security-critical functions. For example, these environments may be used for sensitive cryptographic operations, to verify integrity, or to support Digital Rights Management. These environments typically have access to some amount of secure storage which is only accessible within that environment.
The mobile OS enables a rich set of functionality by supporting the use of mobile applications written by third-party developers. Accordingly, it is common for mobile applications to be sandboxed in some manner to prevent unexpected and unwanted interaction between the system, its applications, and those applications’ respective data (including user data). Mobile applications may be written in native code running closely to the hardware, in interpreted languages, or in high-level web languages. The degree of functionality of mobile applications is highly dependent upon the application programming interfaces (APIs) exposed by the mobile OS.